Key encryption key (KEK): is an encryption key whose function it is to encrypt and decrypt the DEK. Key management application program interface (KM API): is an application interface that is designed to securely retrieve and pass along encryption keys from a key management server to the client requesting the keys. Aug 08, 2018 If we generate a 16-byte output (32 hex characters), we have a 128-bit key, and a 32-byte output (64 hex characters) will generate a 256-bit key. HKDF is used in TLS 1.3 for generating encryption.
- Used To Generate An Encryption Key Mean
- Generate Pgp Key Windows
- Encryption Key Management Procedure
- Public Key Encryption
- Used To Generate An Encryption Key Download
- Used To Generate An Encryption Keys
The Java KeyGenerator class (javax.crypto.KeyGenerator) is used to generate symmetric encryption keys. A symmetric encryption key is a key that is used for both encryption and decryption of data, by a symmetric encryption algorithm. In this Java KeyGenerator tutorial I will show you how to generate symmetric encryption keys.
Creating a KeyGenerator Instance
The concept of Split Knowledge applies to any access or handling of unprotected cryptographic material like encryption keys or passphrases used to create encryption keys, and requires that no one person know the complete value of an encryption key. If passphrases are used to create encryption keys, no one person should know the entire passphrase. If you use encryption to store data then you generate the IV using CryptGenRandom (or its.net equivalent RandomNumberGenerator.GetBytes) and save it along the document (in clear, no need to protect the IV). You never write down the key, the key is provided by the user. About RandomKeygen. Our free mobile-friendly tool offers a variety of randomly generated keys and passwords you can use to secure any application, service or device. Simply click to copy a password or press the 'Generate' button for an entirely new set. Password Recommendations. Oct 18, 2016 The encryption keys generated in modern cryptographic algorithms are generated depending upon the algorithm used. Primarily there are two types of encryption schemes: Symmetric and Asymmetric(Public Key encryption). Microsoft generates a Key Encryption Key using the user's password. This KEK is then used to encrypt what they call the Master Key. The Master Key is really a Data Encryption Key. It will be used to encrypt any data that is put in the user's protected storage. Key management for Full Disk Encryption will also work the same way.
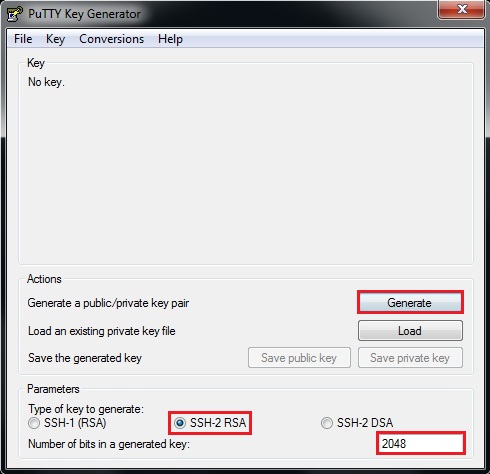
Before you can use the Java KeyGenerator class you must create a KeyGenerator instance. You create a KeyGenerator instance by calling the static method getInstance() passing as parameter the name of the encryption algorithm to create a key for. Here is an example of creating a Java KeyGenerator instance:
This example creates a KeyGenerator instance which can generate keys for the AES encryption algorithm.
Initializing the KeyGenerator
After creating the KeyGenerator instance you must initialize it. Initializing a KeyGenerator instance is done by calling its init() method. Here is an example of initializing a KeyGenerator instance:
So we use jetty to convert our pkcs12 into jks format.OpenSSL for Windows is available from.Keystore to be created: keystore.pkcs12, Certificate File: test.cert.pem, PrivateKey File: test.key.pem.openssl pkcs12 -export -out keystore.pkcs12 -in test.cert.pem -inkey test.key.pemEnter the appropriate password. Now using jetty we can convert the pkcs12 keystore into jks keystore (keystore.jks).java -cp c:jettylibjetty-6.1.1.jar org.mortbay.jetty.security.PKCS12Import keystore.pkcs12 keystore.jksNow to create truststore file.keytool -import -alias test -file test.cert.pem -keystore truststorewhere truststore is the new TrustStore in jks format. Thus we need to use OpenSSL for this but OpenSSL creates the keystore in pkcs12 format.
The KeyGeneratorinit() method takes two parameters: The bit size of the keys to generate, and a SecureRandom that is used during key generation.
Used To Generate An Encryption Key Mean
Generating a Key
Once the Java KeyGenerator instance is initialized you can use it to generate keys. Generating a key is done by calling the KeyGeneratorgenerateKey() method. Here is an example of generating a symmetric key:
Right 1
-->Deleting and recreating encryption keys are activities that fall outside of routine encryption key maintenance. You perform these tasks in response to a specific threat to your report server, or as a last resort when you can no longer access a report server database.
Recreate the symmetric key when you believe the existing symmetric key is compromised. You can also recreate the key on a regular basis as a security best practice.
Delete existing encryption keys and unusable encrypted content when you cannot restore the symmetric key.
Recreating Encryption Keys
If you have evidence that the symmetric key is known to unauthorized users, or if your report server has been under attack and you want to reset the symmetric key as a precaution, you can recreate the symmetric key. When you recreate the symmetric key, all encrypted values will be re-encrypted using the new value. If you are running multiple report servers in a scale-out deployment, all copies of the symmetric key will be updated to the new value. The report server uses the public keys available to it to update the symmetric key for each server in the deployment.
You can only recreate the symmetric key when the report server is in a working state. Recreating the encryption keys and re-encrypting content disrupts server operations. You must take the server offline while re-encryption is underway. There should be no requests made to the report server during re-encryption.
You can use the Reporting Services Configuration tool or the rskeymgmt utility to reset the symmetric key and encrypted data. For more information about how the symmetric key is created, see Initialize a Report Server (SSRS Configuration Manager).
That's how much we trust our unbeatable service. 
How to recreate encryption keys (Reporting Services Configuration Tool)
Generate Pgp Key Windows
Disable the Report Server Web service and HTTP access by modifying the IsWebServiceEnabled property in the rsreportserver.config file. This step temporarily stops authentication requests from being sent to the report server without completely shutting down the server. You must have minimal service so that you can recreate the keys.
If you are recreating encryption keys for a report server scale-out deployment, disable this property on all instances in the deployment.
Open Windows Explorer and navigate to drive:Program FilesMicrosoft SQL Serverreport_server_instanceReporting Services. Replace drive with your drive letter and report_server_instance with the folder name that corresponds to the report server instance for which you want to disable the Web service and HTTP access. For example, C:Program FilesMicrosoft SQL ServerMSRS10_50.MSSQLSERVERReporting Services.
Open the rsreportserver.config file.
For the IsWebServiceEnabled property, specify False, and then save your changes.
Start the Reporting Services Configuration tool, and then connect to the report server instance you want to configure.
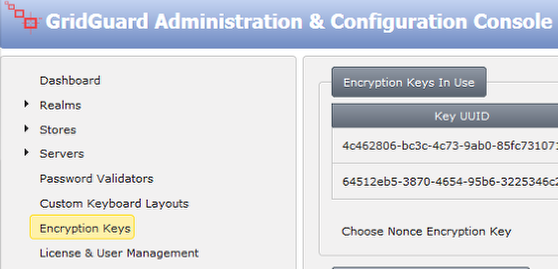
On the Encryption Keys page, click Change. Click OK.
Restart the Report Server Windows service. If you are recreating encryption keys for a scale-out deployment, restart the service on all instances.
Re-enable the Web service and HTTP access by modifying the IsWebServiceEnabled property in the rsreportserver.config file. Do this for all instances if you are working with a scale out deployment.
How to recreate encryption keys (rskeymgmt)
Disable the Report Server Web service and HTTP access. Use the instructions in the previous procedure to stop Web service operations.
Run rskeymgmt.exe locally on the computer that hosts the report server. Use the -s argument to reset the symmetric key. No other arguments are required:
Restart the Reporting Services Windows service.
Deleting Unusable Encrypted Content
If for some reason you cannot restore the encryption key, the report server will never be able to decrypt and use any data that is encrypted with that key. To return the report server to a working state, you must delete the encrypted values that are currently stored in the report server database and then manually re-specify the values you need.
Deleting the encryption keys removes all symmetric key information from the report server database and deletes any encrypted content. All unencrypted data is left intact; only encrypted content is removed. When you delete the encryption keys, the report server re-initializes itself automatically by adding a new symmetric key. The following occurs when you delete encrypted content:
Connection strings in shared data sources are deleted. Users who run reports get the error 'The ConnectionString property has not been initialized.'
Stored credentials are deleted. Reports and shared data sources are reconfigured to use prompted credentials.
Reports that are based on models (and require shared data sources configured with stored or no credentials) will not run.
Subscriptions are deactivated.
Once you delete encrypted content, you cannot recover it. You must re-specify connection strings and stored credentials, and you must activate subscriptions.
You can use the Reporting Services Configuration tool or the rskeymgmt utility to remove the values.
How to delete encryption keys (Reporting Services Configuration Tool)
Start the Reporting Services Configuration tool, and then connect to the report server instance you want to configure.
Click Encryption Keys, and then click Delete. Click OK.
Restart the Report Server Windows service. For a scale-out deployment, do this on all report server instances.
How to delete encryption keys (rskeymmgt)
Run rskeymgmt.exe locally on the computer that hosts the report server. You must use the -d apply argument. The following example illustrates the argument you must specify:
Restart the Report Server Windows service. For a scale-out deployment, do this on all report server instances.
Encryption Key Management Procedure
How to re-specify encrypted values
Public Key Encryption
For each shared data source, you must retype the connection string.
For each report and shared data source that uses stored credentials, you must retype the user name and password, and then save. For more information, see Specify Credential and Connection Information for Report Data Sources.
For each data-driven subscription, open each subscription and retype the credentials to the subscription database.
For subscriptions that use encrypted data (this includes the File Share delivery extension and any third-party delivery extension that uses encryption), open each subscription and retype credentials. Subscriptions that use Report Server e-mail delivery do not use encrypted data and are unaffected by the key change.
Used To Generate An Encryption Key Download
See Also
Used To Generate An Encryption Keys
Configure and Manage Encryption Keys (SSRS Configuration Manager)
Store Encrypted Report Server Data (SSRS Configuration Manager)